Financial Services must manage risks such as ransomware, insider threats and regulatory compliance demands. To achieve this, using tools ZTNA, XDR and FWaaS (typically bundled into SD-WAN/SASE), can mitigate potential risks. |

The financial services sector has been in the eye of the cybersecurity storm for many years. However, 2021 saw unprecedented cyber-attacks. The banking industry, for example, experienced a staggering 1,318% increase in ransomware attacks during the year. The ENISA Threat Landscape Report 2021 describes the situation as this “the cybersecurity landscape has grown in terms of sophistication of attacks, their complexity and their impact.” The cost of doing nothing is, on average, around $18.9 million (£13.9 million) according to a 2021 IBM study.
The financial service sector is naturally distributed through its branch culture. But as the sector increases its digitisation of services and products, and as ‘anywhere working’ normalises, the sector presents a smorgasbord of opportunity for cybercriminals and fraudsters.
Information about the choices needed to mitigate these cyber threats can empower IT decision makers in the financial services sector. But how do you make sure that a decision is the best one? As SD WAN and cybersecurity continue to converge, how can those keeping financial services secure, ensure that the whole is greater than the sum of the parts?
Financial services in cybersecurity covers the following business types:
- Commercial Banks
- Investment Banks
- Insurance Businesses
- Mutual Funds Credit Unions
- CPA Firms Wealth Management
How cloud-first became a financial services cybersecurity challenge?
The mix of digital transformation, an expanded workforce, regulation updates and new laws, alongside an ever-expanding vendor ecosystem, has created a perfect storm for financial services and the threats that FIs face. A conundrum has appeared: a cloud-first organisation needs to accommodate a distributed workforce, but this places the organisation at an increased risk of cybersecurity attacks – together, they push a FI out of sync with regulations.
The SD WAN was developed because networks are no longer an island. But SD WAN is not a cybersecurity solution either. SD WAN must be augmented with layers of robust effective security to provide the sophisticated security stack needed in financial services, a sector that must manage a multitude of solutions and vendors.
However, the technology landscape is never at rest. As events have conspired to increase cyber risk, technology has responded. The result is that financial sector IT decision-makers are often swamped by options. The sector is also one of the most heavily regulated: FCA fines in 2021, reached £567,765,219. Compliance in the sector is complex, time-consuming, and costly: financial services must handle a perfect storm of cost and complexity. The cost to FIs across the world, of compliance with financial crime regulations, is, according to a LexisNexis report “Global True Cost of Compliance 2020”, $213.9 billion.
Cybersecurity augmentation of an SD WAN platform is best achieved through security-by-design and deep integration with appropriate solutions. This ecosystem view is based on a tightly meshed SD WAN cybersecurity solution, a view encapsulated in Gartner’s SASE framework (Secure Access Service Edge).
Read more on the SASE Framework here: What is the Gartner SD WAN SASE security model?
Budgets to deal with this evolving IT challenge only seem to increase: a survey into IT spend in financial services by the Enterprise Strategy Group found that 55% of respondents expect to increase their budget; how best to spend this budget is the question? Having a strong evaluation strategy is the foundation stone of good decisions.
Evaluation considerations of SD WAN for financial services within the context of Cybersecurity
An IDC 2020 report, Five Key Enterprise Networking Trends to Watch in 2020, predicted that 95% of respondents would be implementing SD WAN in the coming two years. This is playing out with the SD WAN market growing by 45% in Q3, 2021. The financial service sector is embracing SD WAN using the technology to simplify and consolidate across a complex environment that has multiple branches and, since the pandemic, work from anywhere. SD WAN provides the reliability needed to ensure business continuity in this busy system. However, financial services are a cyber target. According to the IBM 2021 “Threat Intelligence Index”, the financial services sector is the #1 most attacked sector. Deploying SD WAN in a high-risk environment means that there must be deep cybersecurity solution integration; in other words, at the levels of digitisation and network expansion of the modern FI, you cannot evaluate an SD WAN solution without considering security.
Read more about SD WAN here: What is SD WAN
Baseline evaluation values:
The starting points for SD WAN and cybersecurity evaluation must encompass:
Design: SD WAN solutions must use a multi-breakout network with security baked into the design – augmented by cybersecurity solutions. These solutions must add the security functionality missing in SD WAN. The distributed nature of FI, within a cloud infrastructure, lends well to the holistic ethos of a zero trust. A Zero trust architecture should be augmented by using solutions such as Web Firewall as a Service, Privileged Access Management (PAM), and Extended Detection and Response (XDR) for distributed endpoints.
Integration: SD WAN must use cybersecurity solutions, deeply integrated into the stack, to provide an ecosystem model of threat prevention. As the FI increasingly moves to a public-cloud infrastructure and delivers apps using an SaaS model, the need for an ecosystem to meet stringent data access regulations and manage massive threat volumes in the FI sector is an essential.
Compliance: This ecosystem approach must have at its core, adherence to the stringent regulations that govern the financial services sector. As cloud is increasingly adopted by the financial service sector and banking, it is easy for a distributed working environment to take an FI out of compliance. Compliance requirements must be mapped to the functional capabilities of an SD WAN-Cybersecurity solution suite.
SD WAN and cybersecurity solutions: the whole is greater than the sum of the parts
- SD WAN needs a secure foundation based on effective cybersecurity solutions
- Augmentation of SD WAN and security requires deep, design-driven, integration
- The network stack and security stack must converge seamlessly to build the optimal solution
- Begin with a zero trust ethos
The principle of ‘zero trust security’ has come into its own during the last two years as the pandemic shifted working environments and opened cybersecurity vulnerabilities. An example of the size of the problem can be seen in an interview between Fintech Futures and RBS. The bank described the scope of the situation, vis-à-vis, home working during the pandemic:
“(on the) 15 May there were nearly 5.5m video conferencing minutes racked up across more than 40,000 meetings. Remote-working levels peaked this week, with 52,000 people logged in remotely on 20 May.”
The urgency of the situation placed zero trust centre stage in the financial service sector. Now, 94% have a zero trust plan in place or expect to work towards zero trust over the next 12-18 months.
Zero trust is a concept first ideated by analyst firm Forester. The principles, based on always-on access verification, have been subsequently developed by the U.S. National Institute of Standards and Technology, NIST. This has resulted in guidance from the organisation, in the form of publication, NIST SP 800-207 ZTA (Zero Trust Architecture). A quote from the publication captures zero trust
“Remote enterprise subjects and assets cannot fully trust their local network connection. Remote subjects should assume that the local (i.e., non-enterprise-owned) network is hostile. Assets should assume that all traffic is being monitored and potentially modified.”
SD WAN must be designed from the ground up to work by the principles of zero trust security through effective cybersecurity solution integration.
The parts:
Zero Trust (ZTNA)
A ZTNA (Zero Trust Network Access) is about developing a trust framework based on verifying access. SD WAN provides the framework for working across a disparate network including remote broadband connections. ZTNA works to provide monitoring and access controls based on zero trust principles across the network, no matter where or what device is used for access. Having a ZTNA framework underpinning the use of SD WAN is ideal for work from anywhere and branch access.
ZTNA uses a discovery and analytics tool to map users to applications. The rules of access can then be handled using a Privileged Access Management (PAM) solution. Applying ‘least privilege’ to resource access is a fundamental tenet of zero trust, i.e., only allowing access to those who need it. This minimises the risk associated with access to data and other network resources. SD WAN integrated with PAM and ZTNA provides ‘default deny’, least privilege access, as per the NIST Risk Management Framework.
Zero trust as a principle enabled using a ZTNA and PAM solution allows FIs to meet regulations around data access and privacy. Data breaches and privacy are an integral part of the culture of banking and the financial service industry. Employees have access to sensitive data and a zero trust policy must be enforced. IT decision makers working within financial services must consider two things in evaluating these solutions:
1. The technology: ZTNA solutions provide the ability to automate zero trust architectures such as create micro-segmentation. These technologies help busy financial IT departments to meet the strict regulations around access control to data and help prevent data breaches.
2. Vendor experience: zero trust architectures can be complex to set up, especially across a public cloud infrastructure. Vendors need to have experience in working with the financial and banking sector.
Visibility, monitoring, policy enforcement
Work anywhere and branch working creates a complex security conundrum for financial services. Visibility, monitoring, and policy enforcement, within this type of expanded network, is a security challenge. The massive attack surface of a financial institution requires deep visibility. And financial sector organisations also must comply with stringent regulations.
Cybersecurity solution integration should include a Cloud Access Security Broker (CASB) to provide the orchestration, visibility, and policy facilitation between devices and the cloud.
A Firewall-as-a-Service (FWaaS) must be integrated into an SD WAN to provide highly granular firewall functionality across every SD WAN appliance; each branch or home office will then have an intrinsic firewall.
Regulations have typically created a complex environment that has affected cloud adoption, especially public cloud. This has been evidenced by a Google Cloud survey based on 1,300 leaders in the FI sector. In response, a European Cloud User Coalition (ECUC) has formed to smooth the adoption of public cloud services in the financial services sector. However, public clouds require additional policies and detection across web access. A Secure Web Gateway (SWG) solution is used to control web access via a remote device, helping in the adoption of a safe public cloud infrastructure.
SWG and WFaaS are important in the FI industry as there must be zero tolerance to data breaches. IT decision makers must consider two things in evaluating these solutions:
- The technology: must provide robust, use intelligent-technologies such as machine learning to provide adaptive URL filtering, and malicious-code detection and filtering. The WFaaS should have deep visibility capabilities and be highly adaptive to handle public-cloud infrastructures.
- Vendor experience: vendors need to have experience in working with the financial and banking sector. Netify is aware of cloud vendors which now offer access to their PasS and IaaS surrounded by an eco-system of pre-selected partners which meet strict financial services compliance regulations.
Endpoints, threat detection and response
At a wide net level, SIEM (security information and event management) provides the event logging and analysis to cover the entire expanded network. A SIEM, however, generates security event alerts to a degree that can be overwhelming, especially in complex environments such as those in the financial services sector. Coupling SIEM with a more granular XDR (Extended Detection and Response) solution provides the next level of visibility needed to focus on the high-risk extended environment of a modern FI. XDR uses smart data analytics via ML (machine learning) to analyse network data, looking for anomalies, patterns, and trends that signal a potential cyber threat or attack. The mix of an XDR with a SIEM capability helps to meet compliance and focus on threats.
To help a busy FI, IT department, maintain security and fill any skills gaps, MDR (Managed Detection and Response) can be added to the armoury. An MDR is used to augment XDR with additional monitoring, threat hunting, and response capabilities from security specialists. MDR is a managed service and is typically connected to a SOC (Security Operations Centre) for analysis and response. IT decision makers must consider two things in evaluating these solutions:
- XDR technology: XDR must be adaptive to work in an ever-changing threat landscape. This is typically achieved by utilising intelligent technologies such as machine learning. The XDR solution should be able to detect both internal (insider threats) and external threats. Technology solutions should be flexible and scalable enough to manage the highly distributed environment of an FI and be configurable enough under high threat volume to minimise false positives.
- Vendor experience: to meet the exacting needs of an FI, vendors must be experienced in working within the sector. The sector is experiencing massive volumes of attacks and any vendor that delivers an XDR/SIEM/MDR solution must be able to handle this volume level.
The whole: where security stack meets network stack: Secure SD WAN
By adding layers of security capability to an SD WAN, this enhanced SD WAN can make sure that a financial service company is both compliant and secure.
FIs face many challenges in the changing nature of cybersecurity threats, working environments, and updates in regulations. Financial sector employees, often work with highly sensitive information, making them targets for cybercriminals. Regulations in the financial service sector are a heavy burden but must be adhered to, in an effort to protect data and the IT infrastructure, and to avoid heavy fines. An FI CXO must walk a tightrope, to ensure that employee access is safe and seamless, whilst maintaining compliance. Financial specific regulations that benefit from a Secure SW WAN include:
- Gramm–Leach–Bliley Act (GLBA): protect customer data by ensuring that data access is denied by default and that security vulnerabilities are detected early.
- Financial Industry Regulatory Authority (FINRA): detect and mitigate cyber-threats.
- Bank Secrecy Act (BSA): helps to detect and reduce insider threats.
A ‘secure SD WAN’, ticks many of the compliance boxes around data protection, data privacy, and cyber-resilience. An SD WAN that is augmented with zero trust technologies, future proofs a FI against changes in regulations and security threats.
Use cases for secure SD WAN in the financial services sector
The financial sector has unique needs in terms of distributed network models. In addition, trusted employees, vendors, and executives, within FIs, are all targeted by cybercriminals looking for gaps in awareness and software vulnerabilities on devices and apps. The pressures from an ‘always on’ industry add to the challenges of securing access across multiple locations, devices, and individuals. A secure SD WAN balances this need, tackling important use cases in the financial sector such as:
Fast, secure, home offices and branches
During the pandemic, some banks such as Credit Suisse had around 90% of employees working from home. This shift happened quickly and the response to make home working safe enough to meet regulations was a challenge. Similarly, getting new branches into a position where they are securely connected can be time-consuming. A secure SD WAN, with integrated zero trust cybersecurity solutions, provides the secure framework to connect home offices and branches to the network. The deployment is centrally managed, devices are securely configured and managed, and access is performed under zero trust conditions.
Data protection and compliance
Anywhere connection through personal and corporate devices requires fast and flexible access control. Access by employees, contractors, vendors, and customers, are disparate and the old idea of perimeter control is long gone. The basic security functionalities of an SD WAN, such as encrypted tunnels, augmented with security from solutions such as ZTNA, SWG, CASB, and a WFaaS, ensure that data is secured against unauthorised access. The same integrated and comprehensive security will help the financial institution meets stringent data protection regulations.
Future-proofing the SD WAN
An SD WAN should be effective in reducing the attack surface, not increasing it. A survey from the FSSCC (Financial Services Sector Coordinating Council), found that financial sector CISOs spent around 40% of their time trying to reconcile cybersecurity with regulatory frameworks. This costly exercise can be streamlined with the right integrated solution suite. Financial services, often considered an early adopter of technologies, are in a unique position. FIs have choices in how to deal with the cyber-threat landscape. When evaluating an SD WAN and/or cybersecurity solution, remember that the whole is greater than the sum of the parts – evaluate for a secure, expanded, modern financial services network that is future-proof enough to handle a fluid regulatory, cybersecurity, and work landscape.
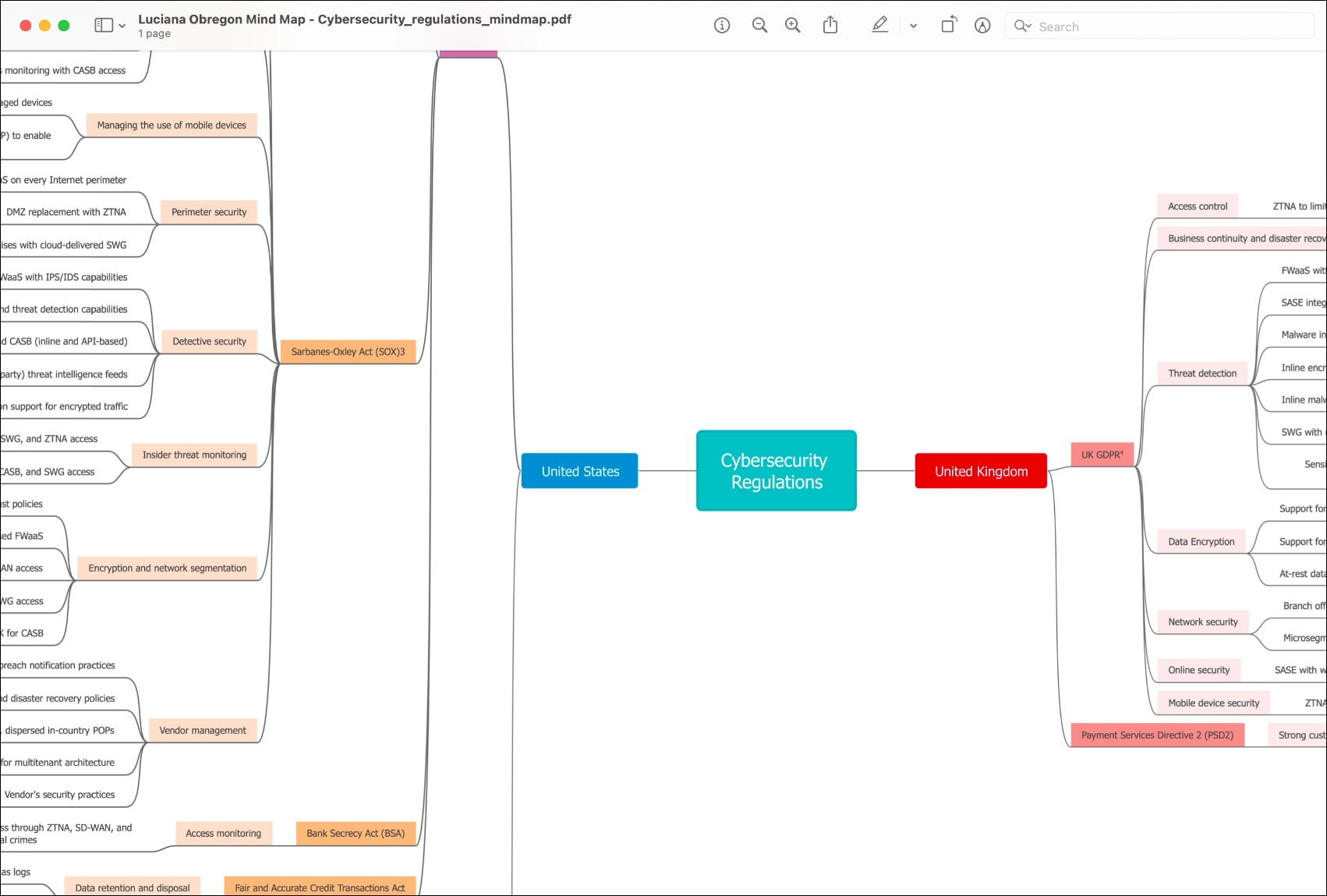
List of financial services cybersecurity regulations
- EU-GDPR The European General Data Protection Regulation (EU-GDPR)
- UK-GDPR The UK General Data Protection Regulation (EU-GDPR)
- NIST The National Institute of Standards and Technology (NIST) is the United State’s equivalent of the International Organization for Standardization (ISO)
- SOX The Sarbanes-Oxley (SOX) act of 2002 is a law passed by U.S Congress to protect investors from financial scams.
- PCI DSS Payment Card Industry (PCI) Data Security Standards (DSS)
- GLBA The Gramm–Leach–Bliley Act (GLBA)
- FINRA The Financial Industry Regulatory Authority (FINRA)
- PSD 2 The Payment Services Directive (PSD 2)


