What are the Cybersecurity regulations and frameworks specific to financial services?
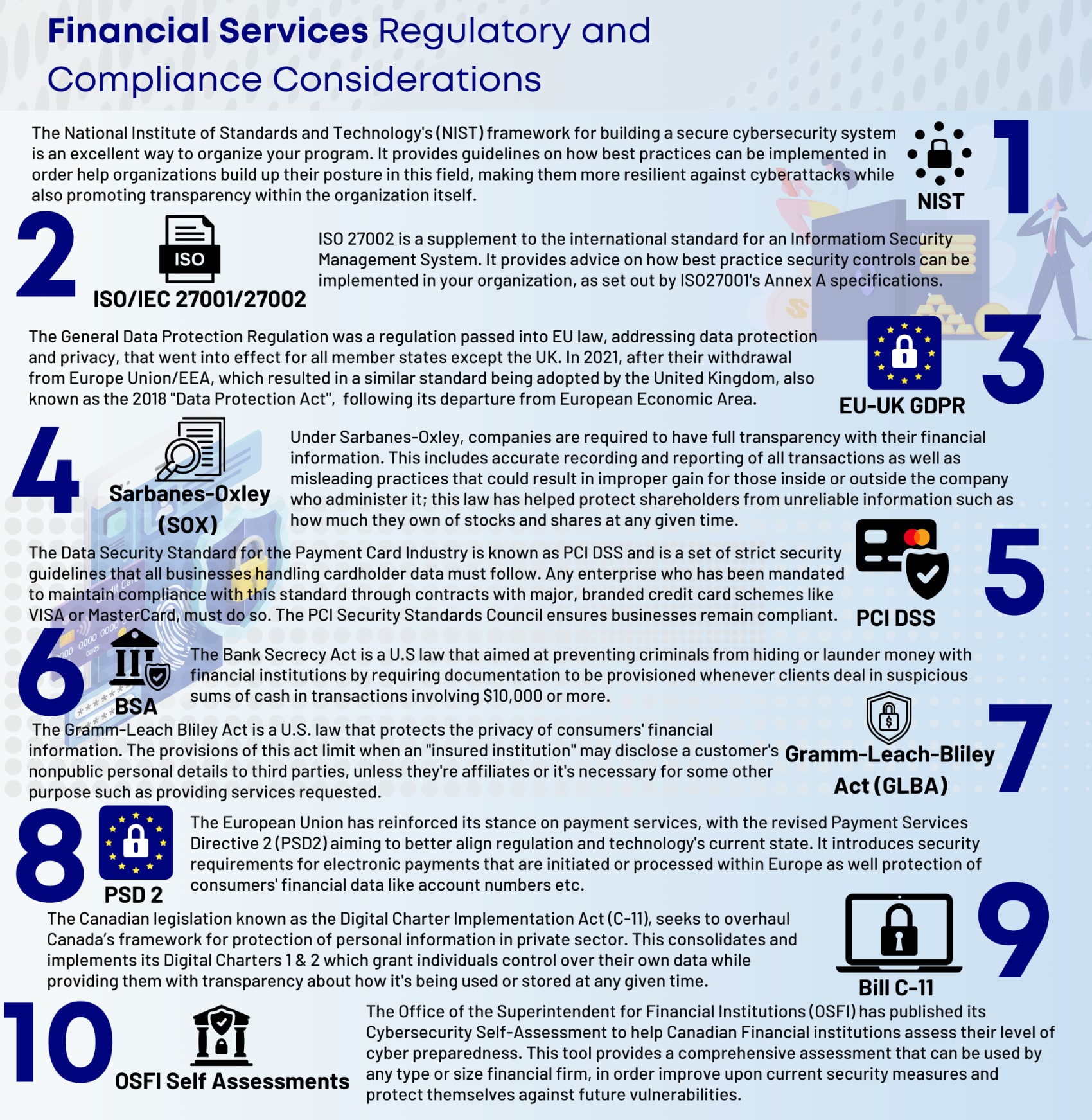
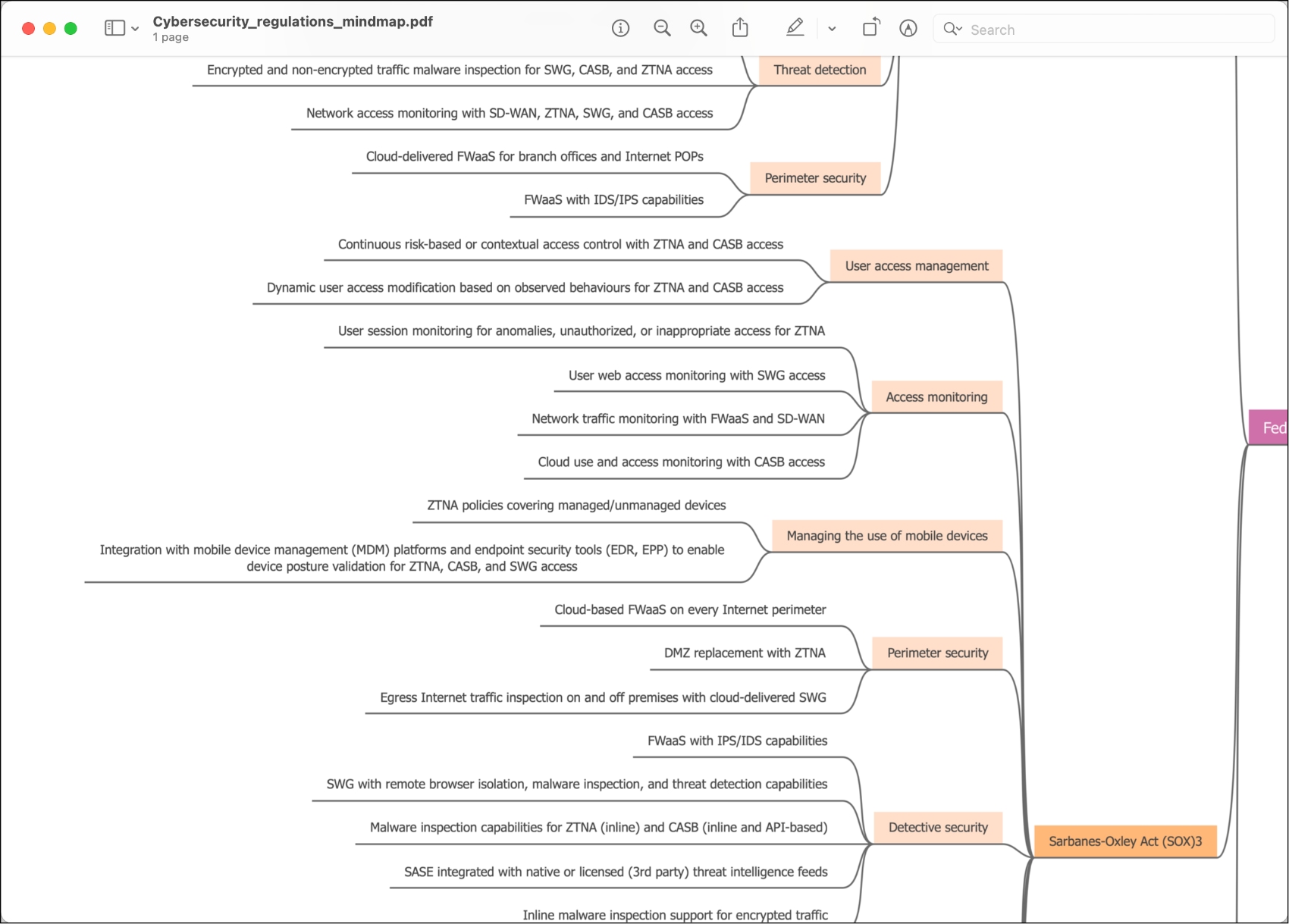
The SOX Framework spawned from The Sarbanes-Oxley (SOX) act of 2002 and is required to be followed by all public companies in the financial sector in the United States. This framework was set up to protect investors from fraud by providing a way to validate the accuracy of financial transactions but has grown to include cybersecurity requirements to help curb common attacks aimed at the financial sector.
Payment Card Industry (PCI) Data Security Standards (DSS) is an international standard with which any business that processes credit card payments must comply. PCI DSS has various levels of certification which carry different security requirements based on an organization’s role in processing card payments. For example, smaller merchants who accept card payments may be able to comply with simple self-assessment questionnaires or undergoing a very basic automated vulnerability scan, while organizations who process or store large amounts of card transaction data may need to be regularly audited by a Qualified Security Assessor (QSA).
Additionally, financial organizations in the European Union must comply with PSD 2 (Payment Services Directive) which includes language on safeguarding digital payments, data integrity and authentication methodology. The Bank Secrecy Act (BSA), which is another United States regulation, requires all financial institutions that accept funds from customers to work with governmental bodies in order to battle crime in the financial sector. BSA has requirements around cybersecurity and managing data breaches in its scope which requires organizations to consider and prepare for potential cyber incidents.
The Gramm-Leach-Billey Act (GLBA) is a privacy regulation specific for financial services and it’s required to be followed by all United States organizations selling financial services or products. GLBA aims to protect the consumer by giving them the right to knowledge of how their data is shared and putting the responsibility of privacy and safe data handling on the processors and organizations handling private data, including financial institutions specifically.
The Financial Industry Regulatory Authority (FINRA) in the United States requires that all brokers and brokerage firms giving financial advice or participating in the trade of securities are licenced and registered. Any broker or brokerage firm licenced under FINRA is subject to compliance with FINRA rules, regulations and regular compliance audits.